AI model provenance refers to the documentation of an AI model’s origin. One can use Thistle’s OTA update system to deploy one or more AI model files to devices, and allow an AI application running on devices to authenticate deployed AI model files before applying them, and thus establishing provenance. In this guide, we walk you through the steps toDocumentation Index
Fetch the complete documentation index at: https://docs.thistle.tech/llms.txt
Use this file to discover all available pages before exploring further.
- digitally sign and publish an AI model file using Thistle Release Helper (TRH), and
- fetch the published AI model file and verify its authenticity using Thistle Update Client (TUC)
Tools needed
- Version 1.7.1 (or above) of TUC and TRH for your platform
- The Thistle Update Client: A binary to run on the device side to obtain the latest OTA update
- The Thistle Release Helper: A CLI developer tool to prepare and publish OTA releases
- One may also try out TUC and TRH on a web browser using Thistle OTA update demo
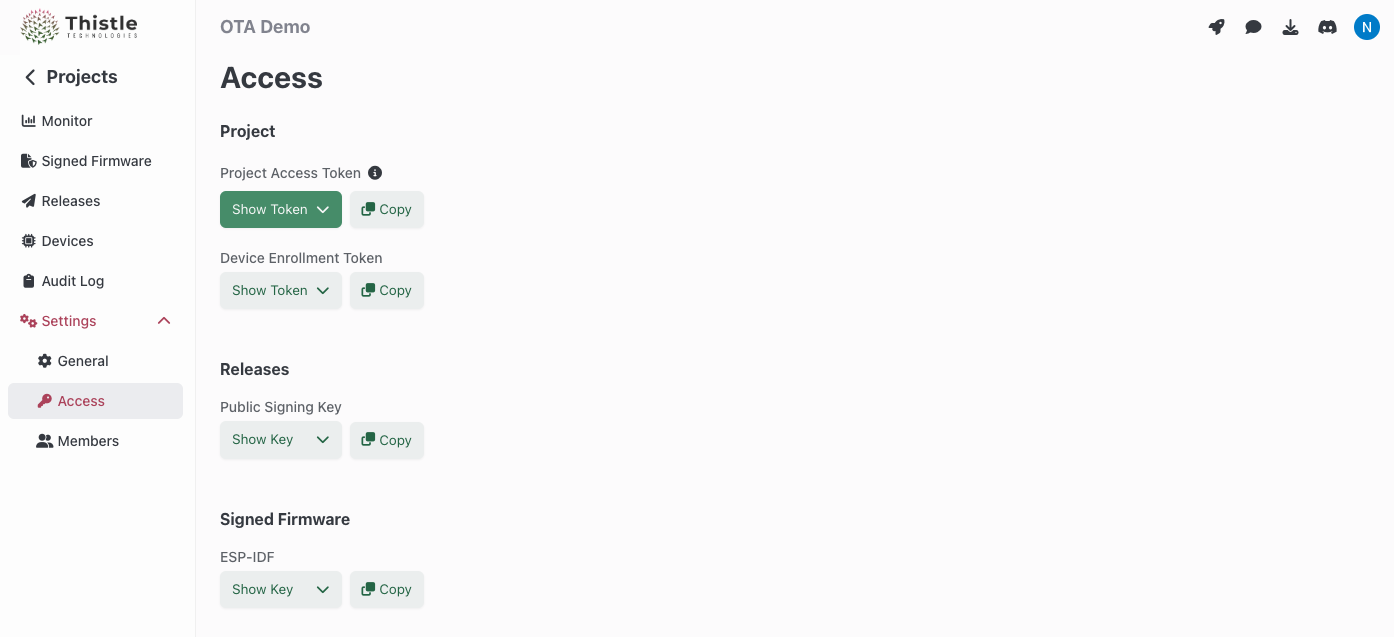
- On the Thistle Control Center App. Visit
the settings section of a project to obtain the API token (“Project Access
Token”) to be used as
THISTLE_TOKENin the configuration step below.
TRH configuration and initialization
Configure your Thistle project’s access token for TRH- Bash
- Windows PowerShell
trh init command. This creates a Cloud-KMS-backed key pair on the Thistle backend;
if a key pair already exists on the backend, the public key portion is returned.
The private key in the key pair is used to sign the OTA update bundle and
AI model files. An OTA update manifest file template manifest.json is
also created locally in the current directory.
Your local working environment is now ready.
Prepare and release a digitally signed AI model file
Package an OTA update bundle containing a dummy AI model file,model.pt, which
will be installed at path /tmp/model.pt on a device.
--sign-ai-model flag is present, trh prepare iterates over all
files under the target release directory, and signs each file using the private
key to create a signature file at /path/to/release/filename.thistlesig, where
/path/to/release/filename is the file to sign. In our case, the signature file
for release/model.pt is created as release/model.pt.thistlesig.
Publish the signed AI model file for OTA update
Release the prepared OTA update bundle including the AI model file and its signature to Thistle backend.Get AI model file with TUC
Create a TUC configuration filetuc-config.json for a device.
tuc-config.json on a device where tuc is run to receive
the AI model. In this guide, we will run tuc on the same machine where trh
is run.
/tmp/model.pt and /tmp/model.pt.thistlesig,
respectively.
Verify AI model in AI application
To verify that the AI model is indeed deployed with Thistle OTA at a specified time, an AI application can call (shell out to)tuc with tuc’s verify-file
subcommand
tuc verify-file to make a
decision on how to proceed.
